...
| Center |
|---|
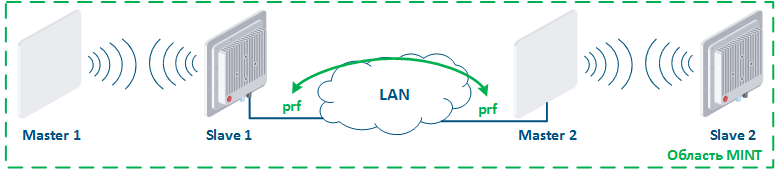
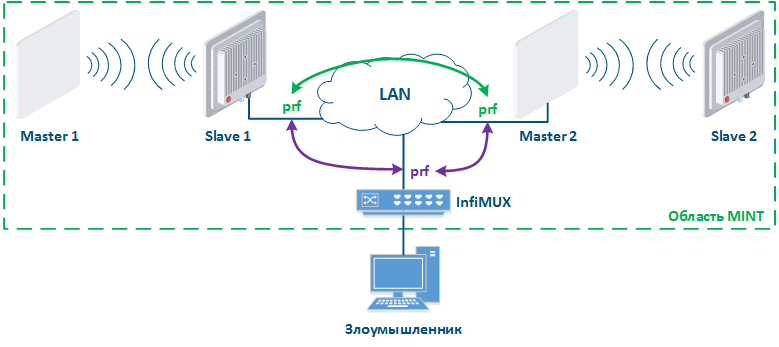
Figure 15a - Joining links in the MINT area Figure 15b - An example of the attack using MINT protocol |
Anchor infrastructure infrastructure
| infrastructure | |
| infrastructure |
...
Infrastructure
Infrastructure security is the important section of information security, which needs a special attention. Infrastructure character depends on the technical policy of the enterprise. The network should contain logging, monitoring and technical accounting.
| Anchor | ||||
|---|---|---|---|---|
|
...
Система мониторинга необходима для централизованного управления устройствами и контроля работы сети. Кроме того, система мониторинга рассылает уведомления инженерам, если значения параметров вышли за рамки разрешённого диапазона. Такие уведомления уменьшают время реакции обслуживающего персонала, благодаря чему минимизируются последствия сбоев и вероятных атак.
Системы мониторинга могут быть интегрированы с системами сигнализации и видеонаблюдения.
Компания Инфинет предоставляет собственную систему мониторинга беспроводных устройств Инфинет - InfiMONITOR. Система мониторинга осуществляет сбор данных следующими способами (рис. 16):
...
Monitoring
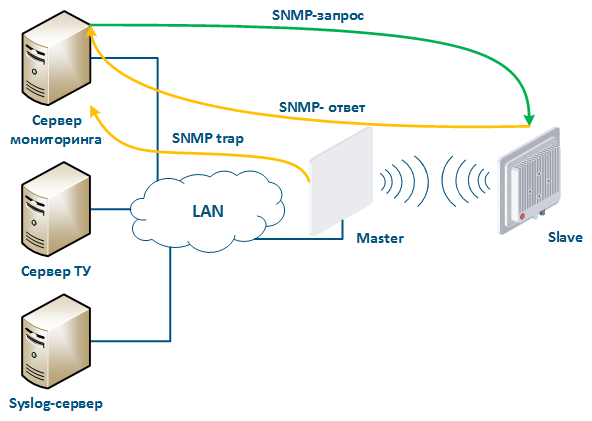
A monitoring system is required for centralized device management and network operation monitoring. Also, the monitoring system sends notifications to engineers if the parameter values are outside the allowed range. Such notifications reduce the service personnel response time, thereby minimize the consequences of failures and possible attacks.
Monitoring systems can be integrated with alarm systems and video surveillance.
Infinet company provides its own system for monitoring Infinet wireless devices - InfiMONITOR. The monitoring system collects data in the following ways (Figure 16):
- Polling: the monitoring system sends SNMP requests to the device demanding the parameters whose values must be received. The device generates an SNMP response for the monitoring system, where it indicates the values of the requested parameters. Device parameters polling is carried out with a set periodicity, which guarantees each device will be requested in a given interval.
- Traps: the device sends a special SNMP Trap message to the monitoring server in case of an incident from the specified list. SNMP Trap sending is initiated by the device itself and occurs instantly, regardless of the polling cycle, however, this will require additional device configuration.
| Center |
|---|
Рисунок 16 - Обмен данными между устройствами и системой мониторинга |
...